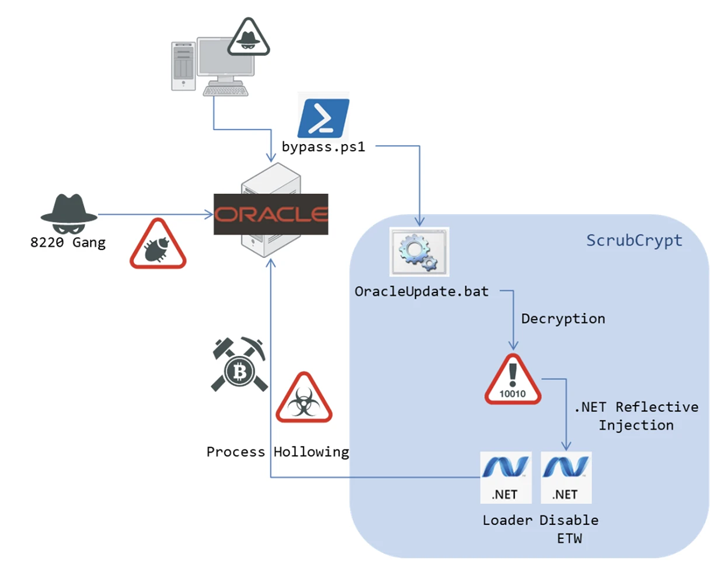
The infamous cryptocurrency miner group called 8220 Gang has been observed using a new crypter called ScrubCrypt to carry out cryptojacking operations.
According to Fortinet FortiGuard Labs, the attack chain commences with successful exploitation of susceptible Oracle WebLogic servers to download a PowerShell script that contains ScrubCrypt.
Crypters are a type of software that can encrypt, obfuscate, and manipulate malware with the goal of evading detection by security programs.
ScrubCrypt, which is advertised for sale by its author, comes with features to bypass Windows Defender protections as well as check for the presence of debugging and virtual machine environments.
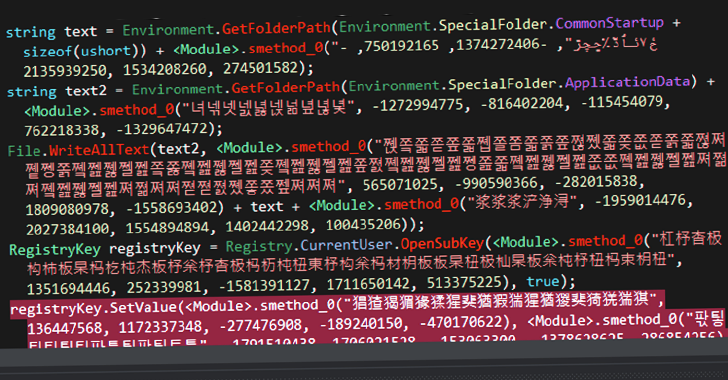
“ScrubCrypt is a crypter used to secure applications with a unique BAT packing method,” security researcher Cara Lin said in a technical report. “The encrypted data at the top can be split into four parts using backslash ‘\.'”
The crypter, in the final stage, decodes and loads the miner payload in memory, thereby launching the miner process.
The threat actor has a track record of taking advantage of publicly disclosed vulnerabilities to infiltrate targets, and the latest findings are no different.
Discover the Hidden Dangers of Third-Party SaaS Apps
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions being granted and how to minimize risk.
The development also comes as Sydig detailed attacks mounted by the 8220 Gang between November 2022 and January 2023 that aim to breach vulnerable Oracle WebLogic and Apache web servers to drop the XMRig miner.
In late January 2023, Fortinet also uncovered cryptojacking attacks that make use of Microsoft Excel documents containing malicious VBA macros that are configured to download an executable to mine Monero (XMR) on infected systems.
(Except for the headline, this story has not been edited by PostX News and is published from a syndicated feed.)