A malicious campaign targeting the Middle East is likely linked to BackdoorDiplomacy, an advanced persistent threat (APT) group with ties to China.
The espionage activity, directed against a telecom company in the region, is said to have commenced on August 19, 2021 through the successful exploitation of ProxyShell flaws in the Microsoft Exchange Server.
Initial compromise leveraged binaries vulnerable to side-loading techniques, followed by using a mix of legitimate and bespoke tools to conduct reconnaissance, harvest data, move laterally across the environment, and evade detection.
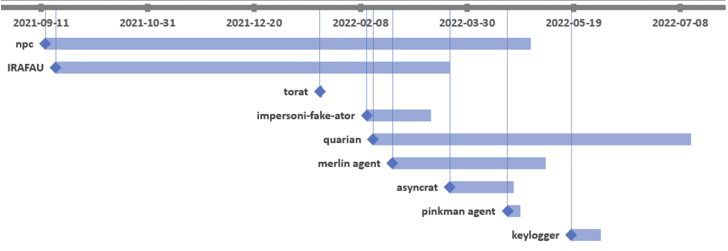
“File attributes of the malicious tools showed that the first tools deployed by the threat actors were the NPS proxy tool and IRAFAU backdoor,” Bitdefender researchers Victor Vrabie and Adrian Schipor said in a report shared with The Hacker News.
“Starting in February 2022, the threat actors used another tool – [the] Quarian backdoor, along with many other scanners and proxy/tunneling tools.”
BackdoorDiplomacy was first documented by ESET in June 2021, with the intrusions primarily aimed at diplomatic entities and telecommunication companies in Africa and the Middle East to deploy Quarian (aka Turian or Whitebird).
The espionage motives of the attack is evidenced by the use of keylogger and PowerShell scripts designed to gather email content. IRAFAU, which is the first malware component delivered after obtaining a foothold, is used to perform information discovery and lateral movement.
This is facilitated by downloading and uploading files from and to a command-and-control (C2) server, launching a remote shell, and executing arbitrary files.
The second backdoor used in the operation is an updated version of Quarian, which comes with a broader set of capabilities to control the compromised host.
Also put to use is a tool dubbed Impersoni-fake-ator that’s embedded into legitimate utilities like DebugView and Putty and is engineered to capture system metadata and execute a decrypted payload received from the C2 server.
The intrusion is further characterized by the use of open source software such as ToRat, a Golang remote administration tool, and AsyncRAT, the latter of which is likely dropped via Quarian.
Bitdefender’s attribution of the attack to BackdoorDiplomacy comes from overlaps in the C2 infrastructure identified as used by the group in prior campaigns.
(Except for the headline, this story has not been edited by PostX News and is published from a syndicated feed.)